Hacking Money Into My Account
Jul 12, 2017 The reality is that accounts are hacked in fairly simple ways — attackers don’t use black magic. Knowledge is power. Understanding how accounts are actually compromised can help you secure your accounts and prevent your passwords from being “hacked” in the first place. Oct 01, 2013 How to hack your own bank account using information on the Internet. By Sabina Datcu, written on October 1, 2013. You just need to know where to look. And the clever identity thief will certainly know where to look. My email address is very easy to find – it's all over the Internet. Or transfer some money to another account, or make a. What happens if your bank account is hacked? Are you liable or is your bank? We have the answer, along with some tips how to keep your money safe online. As society’s reliance on technology grows, especially for things like banking, we will continue to see more and more issues with account hacking. 7 steps to hack into someone’s bank account. 7 Steps to hack a bank account. The experiment: Herbert Thompson. in 2008 wanted to show the public how easy it was to access someone’s personal information and bank account. He did the experiment on someone who he barely knew, a girl named Kim.
People talk about their online accounts being “hacked,” but how exactly does this hacking happen? The reality is that accounts are hacked in fairly simple ways — attackers don’t use black magic.
Knowledge is power. Understanding how accounts are actually compromised can help you secure your accounts and prevent your passwords from being “hacked” in the first place.
Reusing Passwords, Especially Leaked Ones
Many people — maybe even most people — reuse passwords for different accounts. Some people may even use the same password for every account they use. This is extremely insecure. Many websites — even big, well-known ones like LinkedIn and eHarmony — have had their password databases leaked over the past few years. Databases of leaked passwords along with usernames and email addresses are readily accessible online. Attackers can try these email address, username, and passwords combinations on other websites and gain access to many accounts.
Reusing a password for your email account puts you even more at risk, as your email account could be used to reset all your other passwords if an attacker gained access to it.
However good you are at securing your passwords, you can’t control how well the services you use secure your passwords. If you reuse passwords and one company slips up, all your accounts will be at risk. You should use different passwords everywhere — a password manager can help with this.
Keyloggers
Bank Account Money Generator
Keyloggers are malicious pieces of software that can run in the background, logging every key stroke you make. They’re often used to capture sensitive data like credit card numbers, online banking passwords, and other account credentials. They then send this data to an attacker over the Internet.
Such malware can arrive via exploits — for example, if you’re using an outdated version of Java, as most computers on the Internet are, you can be compromised through a Java applet on a web page. However, they can also arrive disguised in other software. For example, you may download a third-party tool for an online game. The tool may be malicious, capturing your game password and sending it to the attacker over the Internet.
Use a decent antivirus program, keep your software updated, and avoid downloading untrustworthy software.
Social Engineering
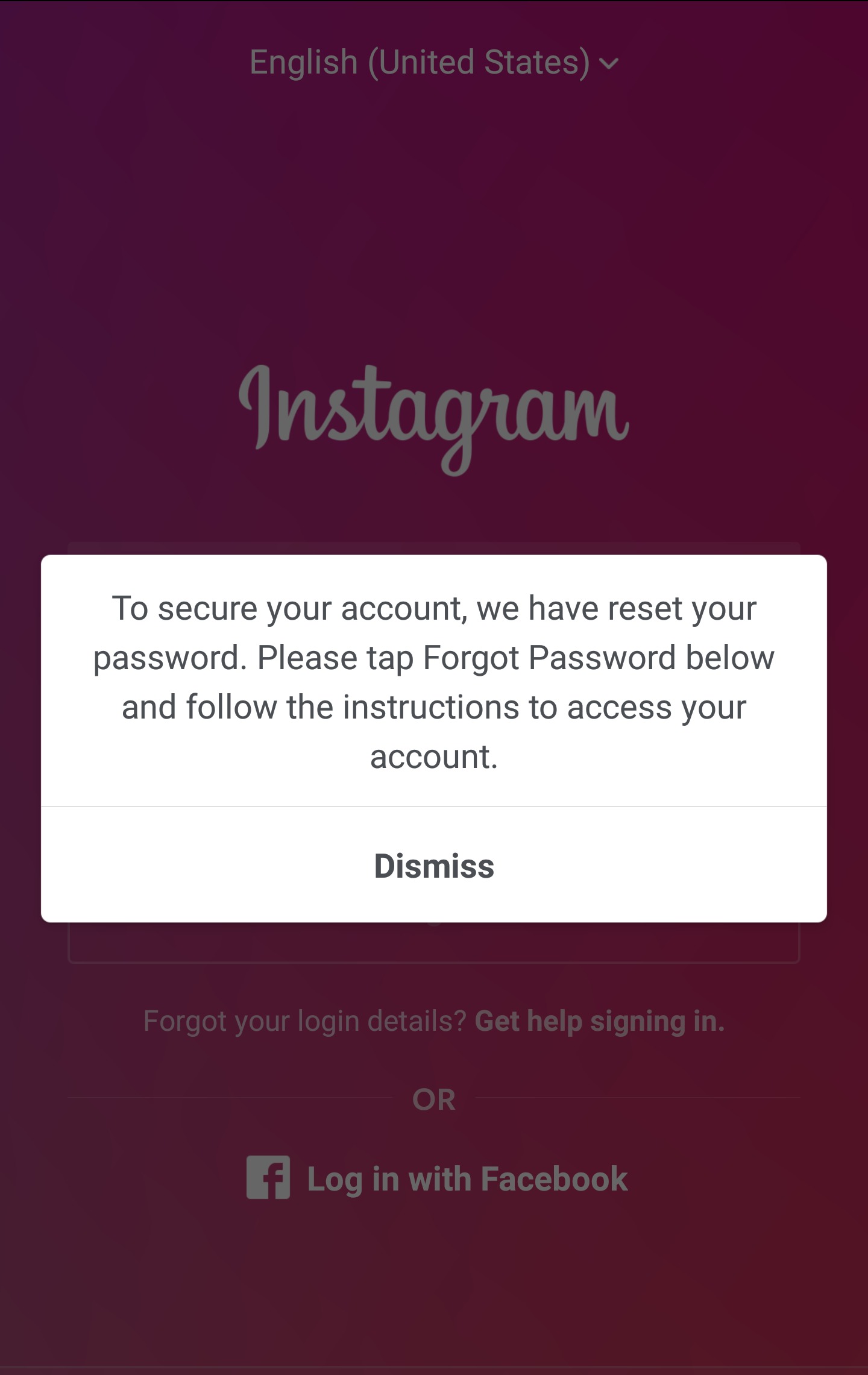
Attackers also commonly use social engineering tricks to access your accounts. Phishing is a commonly known form of social engineering — essentially, the attacker impersonates someone and asks for your password. Some users hand their passwords over readily. Here are some examples of social engineering:
- You receive an email that claims to be from your bank, directing you to a fake bank website and asking you to fill in your password.
- You receive a message on Facebook or any other social website from a user that claims to be an official Facebook account, asking you to send your password to authenticate yourself.
- You visit a website that promises to give you something valuable, such as free games on Steam or free gold in World of Warcraft. To get this fake reward, the website requires your username and password for the service.
Be careful about who you give your password to — don’t click links in emails and go to your bank’s website, don’t give away your password to anyone who contacts you and requests it, and don’t give your account credentials to untrustworthy websites, especially ones that appear too good to be true.
Answering Security Questions
Passwords can often be reset by answering security questions. Security questions are generally incredibly weak — often things like “Where were you born?”, “What high school did you go to?”, and “What was your mother’s maiden name?”. It’s often very easy to find this information on publicly-accessible social networking sites, and most normal people would tell you what high school they went to if they were asked. With this easy-to-get information, attackers can often reset passwords and gain access to accounts.
Ideally, you should use security questions with answers that aren’t easily discovered or guessed. Websites should also prevent people from gaining access to an account just because they know the answers to a few security questions, and some do — but some still don’t.
Windows add font windows 10 is using. To do that, right-click on the right panel and select “New String Value.” Name the string value as “01” and press Enter. If you already have a value with “01,” then name it something else like “02.” Just make sure that all the values have unique numbers.4.
Email Account and Password Resets
If an attacker uses any of the above methods to gain access to your email accounts, you’re in bigger trouble. Your email account generally functions as your main account online. All other accounts you use are linked to it, and anyone with access to the email account could use it to reset your passwords on any number of sites you registered at with the email address.
For this reason, you should secure your email account as much as possible. It’s especially important to use a unique password for it and guard it carefully.
Bluetooth hack download. Apr 12, 2011 Super Bluetooth Hack is one such software that is designed to hack into a mobile phone. This software uses Bluetooth AT commands to get access to target device and read its contents. Super Bluetooth hacks can be used to read SMS message, contacts, start or shutdown, make calls on a less secure target mobile phone. Download Super Bluetooth hack. Bluetooth hack free download - Hack the Universe, Bluetooth Software Ver.6.0.1.4900.zip, Bluetooth 2.0Broadcom Bluetooth Driver and Applicationv6.0.1.4900.zip, and many more programs.
What Password “Hacking” Isn’t
Most people likely imagine attackers trying every single possible password to log into their online account. This isn’t happening. If you tried to log into someone’s online account and continued guessing passwords, you would be slowed down and prevented from trying more than a handful of passwords.
If an attacker was capable of getting into an online account just by guessing passwords, it’s likely that the password was something obvious that could be guessed on the first few tries, such as “password” or the name of the person’s pet.
Attackers could only use such brute-force methods if they had local access to your data — for example, let’s say you were storing an encrypted file in your Dropbox account and attackers gained access to it and downloaded the encrypted file. They could then try to brute-force the encryption, essentially trying every single password combination until one works.
People who say their accounts have been “hacked” are likely guilty of re-using passwords, installing a key logger, or giving their credentials to an attacker after social engineering tricks. They may also have been compromised as a result of easily guessed security questions.
If you take proper security precautions, it won’t be easy to “hack” your accounts. Using two-factor authentication can help, too — an attacker will need more than just your password to get in.
Image Credit: Robbert van der Steeg on Flickr, asenat on Flickr
READ NEXT- › Did Linux Kill Commercial Unix?
- › How to Use Port Knocking on Linux (and Why You Shouldn’t)
- › What Is a “Hot Take,” and Where Did the Phrase Come From?
- › How Windows 7’s “Extended Security Updates” Will Work
- › Windows 10’s Phone Calls Will Support All Android 7+ Phones
Think you’ve secured your PayPal account so that hackers can’t hijack it and steal money from your bank account? Well, guess again, as there are ways of getting into your account and PayPal doesn’t appear to have the means or policies to stop them.
Well known cybersecurity expert Brian Krebs says he discovered these flaws after his own account was broken into twice on Christmas Eve, even after he managed to regain access to it.
DON’T MISS: Possible iPhone 7 Plus leak may reveal two of the phone’s biggest new features
Even though Krebs is often a target of hackers who hate how he exposes their work, the fact that his PayPal account was hijacked indicates that nobody is safe, no matter how Internet-savvy they are. And it seems that it’s PayPal’s security to blame.
One more important point to note is that hackers likely used information about Krebs that’s publicly available to social engineer this hack, so chances are it won’t happen to regular Joes and Janes, assuming their personal data including Social Security numbers and credit cards aren’t out in the open. But, again, it’s PayPal’s job not to allow this kind of breach.
It seems that the hackers did not use malware or any advanced virus programs to steal Krebs’ PayPal account and password. They simply called in, offered the SSN and the four numbers of an old credit card account, and got in.
“On Christmas Eve morning, I received an email from PayPal stating that an email address had been added to my account,” Krebs explained in a detailed post on the matter. “I immediately logged into my account from a pristine computer, changed the password, switched my email address back to the primary contact address, and deleted the rogue email account.”
“I then called PayPal and asked how the perpetrator had gotten in, and was there anything else they could do to prevent this from happening again?” Krebs continued. “The customer service person at PayPal said the attacker had simply logged in with my username and password, and that I had done everything I could in response to the attack. The representative assured me they would monitor the account for suspicious activity, and that I should rest easy.”
“Twenty minutes later I was outside exercising in the unseasonably warm weather when I stopped briefly to check email again: Sure enough, the very same rogue email address had been added back to my account. But by the time I got back home to a computer, my email address had been removed, and my password had been changed. So much for PayPal’s supposed ‘monitoring;’ the company couldn’t even spot the same fraudulent email address when it was added a second time,” he added.
PayPal then locked the account as soon as hackers tried to wire money to an email account belonging to Junaid Hussain, a 17-year-old hacker from Team Poison who joined ISIS and who is believed to have been killed in a U.S. drone strike in 2015.
But then PayPal asked Krebs to provide a photocopy of a driver’s license to regain access to his account – but during the second attack, hackers removed Krebs’s details from the account so that he couldn’t regain control of it.
In his article Krebs explains that PayPal seems to lack the necessary security measures that would make it harder for hackers to steal account credentials, suggesting that further updates would be needed so that attackers would not be able to social engineer their way into an account with the help of information that may be found or sold online.
“I asked the PayPal supervisor why the company couldn’t simply verify my identity by sending a text message to my phone, or a special signal to a PayPal mobile app?” Krebs wrote. “After all, PayPal has had the same mobile number of mine on file for years (the attacker also deleted that number from my profile as well). The supervisor explained that the company didn’t have any mobile authentication technologies and that in order to regain access to the funds in my account I had to send the company a photocopied or scanned copy of my driver’s license.”
Hacking Money Into My Account Yahoo
Driver’s licenses and any other similar documents can be easily forged Krebs argues, making it a futile protection layer.
“Longer term, PayPal should review which of its users have already provided mobile phone information, and then seek to validate those contact numbers,” Krebs argued. “Once that process is done, PayPal can start upgrading its authentication systems — and hopefully become less reliant on static (read: already-compromised) identifiers to validate customers. This would help cut down on account takeovers and reduce the threat of costly, fraudulent credit card donations via hacked accounts.”
“Until then, PayPal will continue to expose its users unnecessarily to security and privacy threats (bear in mind that a crook who gains access to your PayPal account can see all of your transactions and financial data from associated bank accounts),” he concluded.
To read Krebs’s full account of his terrible PayPal experience, follow the source link.
UPDATE: A PayPal spokesperson reached out to BGR with the following statement on the matter: “The safety and security of our customers’ accounts, data and money is PayPal’s highest priority. Due to our privacy policies that protect our customers, PayPal does not publicly disclose details about our customers’ accounts or their specific cases. However, it appears that our standard procedures were not followed in this case. While the funds remained secure, we are sorry that this unacceptable situation arose and we are reviewing the matter in order to prevent it from happening again.”